OK folks, call it what you want we’ve had a glorious data breach but accidental this time.
Not on the scale of Yahoo! where the US equivalent of GCHQ forced the company to include a backdoor on their servers to allows the US National Security Agency unfettered access to your BTInternet email and any other Yahoo! provide email. That was over 1 billion email accounts.
But it would be prudent to change as many online passwords as you can this weekend and subsequently. The potential list of compromised web sites runs to a 22.6M zipped text file that this person has compiled here.
My personal recommendation is to use a password manager which you store on your PC in conjunction with DropBox, OneDrive or your Google Drive. I personally recommend KeePass. It’s available for Mac, Windows and Linux. It’s also available on your mobile phone as well but some folks may need help setting that up so it links with your PC copy of the encrypted passwords stored on DropBox, OneDrive or your Google Drive.
If you have the inclination and want to learn more about protection your online accounts have a look at this site https://twofactorauth.org/ Please follow totnesIT on twitter where I’ll be posting more on how to do this.
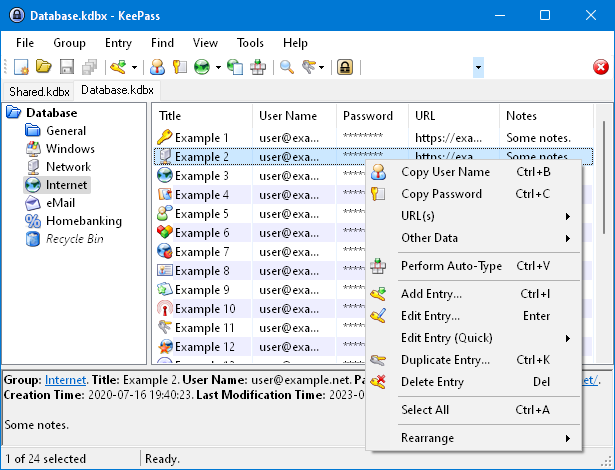
What KeePass looks like on a computer
If you are still reading… This person goes into a bit more detail
https://medium.com/@octal/cloudbleed-how-to-deal-with-it-150e907fd165#.wlv8f5eb4
Octal on Medium writes:
The duration (2016–09–22 to 2017–02–20) and potential breadth of information exposed is huge — Cloudflare has over 2 million websites on its network, and data from any of these is potentially exposed. Cloudflare has said the actual impact is relatively minor, so I believe only limited amounts of information were actually disseminated. Essentially, broad range of data was potentially at risk, but the risk to any individual piece of data was very low. Regardless, unless it can be shown conclusively that your data was NOT compromised, it would be prudent to act as if it were.
While Cloudflare’s service was rapidly patched to eliminate this bug, data was leaking constantly before this point — for months. Some of this data was cached publicly in search engines such as Google, and is being removed. Other data might exist in other caches and services throughout the Internet, and obviously it is impossible to coordinate deletion across all of these locations. There is always the potential someone malicious discovered this vulnerability independently and before Tavis, and may have been actively exploiting it, but there is no evidence to support this theory.



This was really useful and we’ll explained, thank you Mark.